One very common theme we see in the industry is: the ‘bad guys’ only do as much work as they need to do to trick us into giving them what they want.
The below email is an example of such a ‘simple’ attack.
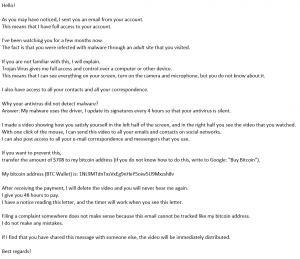
What is happening here?
The bad guy is simply sending an email out to 1000s of email addresses they have to see if someone takes the bait. That is why they call it ‘phishing’. In this case, there is no targeted info about the people, they just send a generic email and see who is tricked into sending them funds.
What if I do happen to go to sites that could be a ‘problem’?
An email like this is almost always a scam. The bad guy knows NOTHING about you and is just ‘fishing/phishing’.
What do I do if I’m concerned about this?
Change your password(s). If a bad guy does have access to your system, a lot of the time it is due to a ‘weak/compromised password’.
Password should be:
- Strong
- Don’t use things people can easily guess about you.
- Do use things easy to remember but hard to guess about you.
- Long
- Longer passwords are always better.
- Different
- Use DIFFERENT passwords for different systems that way if one is compromised it is only compromised in one place.
A good password is = FrogsAreGreen(23)
A bad password is = LetMeIn
I’m still worried, what do I do?
Contact NGT, we are glad to provide some advise as to how to proceed.
Use this link: http://www.ngthelp.com to email, chat, or call!
